Authenticating who’s truly in the back of any action, whether logging into Twitter or getting access to a financial institution account, is the largest mission in safety nowadays.
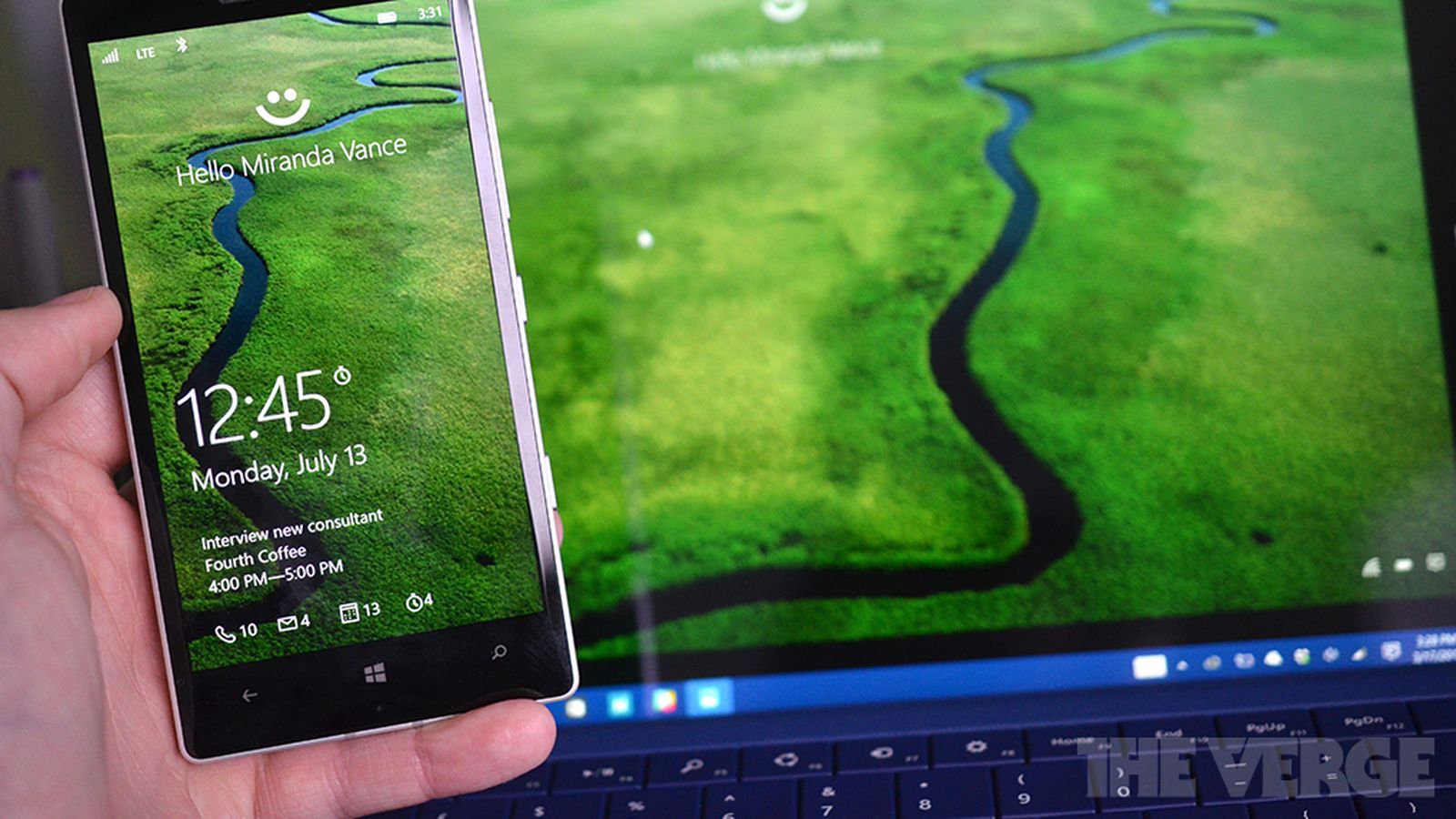
Mobile Devices
Mobile Bay
On the organization degree, this truth is infinitely more critical: agencies want to relax, get admission to their structures and records, and be positive that the most effective individuals who are granted get entry. At the same time, groups must also make sure their employees can paint as productively as possible, and regular and stringent safety protections would surely get them in the manner of “enterprise as regular.” Those conditions create a dichotomy that corporations and protection experts have struggled to triumph over.
Up to now, PINS, passwords, and OTP hardware have been the compromise of preference: sufficient to authenticate a user’s access, however, no longer so burdensome that employees can’t accomplish their jobs. The hassle? They don’t work. In 2016, the five largest records breaches – consisting of headline-making cases like Yahoo! And the DNC- worried about compromised, vulnerable, or reused passwords. That’s more than troubling- a call for a complete security reset.
READ MORE :
- The way to Create a Minimalist Computing device to Be Happy with
- Cell protection: The fact of malware … augmented
- Kids Are Spending More Time On Mobile Devices Than Ever Before
- The world is starting to solve its problems — with or without Trump
- A study reveals that 25 percent of economic provider workers’ cellular gadgets are unpatched
A protection overhaul is an expensive and scary prospect for most enterprises: assessing vendors, buying and deploying new software programs and hardware, and growing and enacting new techniques. Unsurprisingly, agencies had been dragging their feet on making the sort of massive exchange. However, many organizations probably don’t realize that funding they’ve already made is also a door to a new stage of safety: Mobile devices.
It does appear perplexing, given the number of safety headaches BYOD and MDM have given agencies during the last decade. However, innate in Mobile hardware is all of the additives needed for a rising and objectively stronger method of organization safety: biometrics. From the camera to the accelerometer to the oft-used TouchID pad, a complete suite of security functions is already at our fingertips:
Fingerprint: We’re all acquainted with fingerprint scanners: first introduced in 2011 at the Motorola Atrix 4G, TouchID and comparable technologies are a de facto hardware function on our Cell devices. First delivered to allow us to skip the lock screen safety passcode, many apps now install it as an authentication degree. Fingerprinting has long been the monstrous biometric software in the bodily and virtual world, so it’s no wonder it is rated the most famous Mobile biometric. And even though there are (founded) worries about spoofing, the extensive industrial deployment and adoption of fingerprint scanners make it an excellent practice for organization biometric protection – although probably best as a part of a multi-component authentication collection.
Face: The popularity of selfies led cell phone tool manufacturers to place cameras on the front of the smartphone; now, organizations can take advantage of this tiny improvement to enforce facial reputation as a worker authentication thing. Facial popularity software programs use algorithms to identify and authenticate distinguishing facial features. Further security features can be installed by requiring lively biometrics – asking a person to grin, nod, or blink to authenticate. Of course, many employees may be wary of taking a selfie in an assembly so that it will do something like get right of entry to their e-mail, so firms have to take word approximately when and the way facial recognition is required for getting right of access to.
Hand reputation: A newer biometric, hand reputation uses the flash and rear, dealing with a camera to take a picture of a person’s four fingerprints – increasing the security degree above regular fingerprint reputation. Additionally, using flash addresses a number of the issues encountered inside the front-facing camera due to the fact there are fewer issues with lights, which can result in faulty studying.
Iris Experiment: Iris scanning displays promise in organization deployments – particularly after the release of the final year of the Samsung Galaxy Be Aware, which was one of the first Cell gadgets to come prepared with an iris scanner. The unlucky death of that device has taken the technology lower back a few steps. Still, rumors that the iPhone might replace TouchID with iris scanning may significantly place this era in rotation again.
Accurate Biometrics
Behavioral: A telephone’s hardware and software carry alongside a set of answers that make ongoing and non-stop authentication feasible. While we’ve been discussing bodily biometrics – the use of parts of a person to identify them – it’s also possible (and more and more promising) to use a person’s movements. A tool’s myriad sensors may measure behavioral biometrics: has the agency moved to a brand new vicinity, has the microphone picked up your voice currently, how is it being carried, does the movement pattern and gait fit yours, while was the last time the digicam captured your face and many others. Via regular, passive statistics series, your phone can be “assured” that it’s Still you to use the device and won’t constantly ask for credentials or log you out; however, if the confidence rating drops below a certain stage, either due to the fact you’ve moved to an unusual area or haven’t used the smartphone in some time, the app might ask you to log in with your physical biometric once more.
Our Cell devices provide that “remaining mile” to empower biometrics. Biometrics offers a sensible solution to the problems of susceptible and beside-the-point authentication answers. At the same time, it is turning inconvenient, human-centric authentication solutions into the latest Mobile gadgets. Convenient biometric authentication allows a business to guide an extra degree of capabilities for its Mobile workers. It can also be included in company Mobility Control (EMM) solutions to permit sturdy security policies to be enforced for Mobile answers. It additionally solves a value headache related to passwords: biometric authentication can reduce password resets, help table requests, and aid calls using as much as 50 percent, in step with Gartner.
There are many matters to not forget on the journey to killing corporation passwords; however, thanks to Mobile devices, hardware doesn’t need to be one among them.
Have a look at the Cellular gadgets and Mobile Security.
Cell devices have persevered to the upward push of their recognition, and the adoption rates are extremely excessive. This stems from the fact that Mobile conversation has become an ordinary affair. For many humans, leading a life without a Cellular telephone could be impossible for many of us to tolerate. Our lives depend on devices for many things, except the most important advantage of providing a method of communique with human beings. Once more, the continuing rise in the degree of adoption of devices has been accompanied by sophistication within the gadgets and their models and the level of functionality attainable with the gadgets.
Currently, SMA, smartphones, and tablets are primarily based on various platforms depending on the producer. This has increased the functionality that can be executed with cell phones to impossible stages, which is persevering with increasing portions added to the devices. Smartphones and tablets accompany customers anywhere they pass, and in everything they do. Mobile phones are now getting access to the internet at exceptional speeds and with very large capabilities, allowing customers to gain access and even manipulate. With such power, Cell phones and devices are adding an entirely distinct perspective to the equation: IT safety. Machines have been a very large hazard, and this has to do with the fact that human beings can get right to entry a whole bulk of assets from their phones. Mobile devices threaten the points saved in them and the networks they’re a part of.
Like how people take complete steps to secure their computer systems, the cell devices must be confirmed. This arises from the reality that the facts and facts accessed and contained in them consist of personal and personal records, pics and contacts, or even records and protection details belonging to monetary money owed and different online corporations. The gadgets, being the lifeline that they’ve come to be, require safety to control and avoid the dangers and threats available. Take a look at the stairs to install location to make sure that Cell protection is guaranteed. It may be beneficial for many Cell gadgets.
Add a Device
The first step must be finding gadgets with excellent or above-average security functions compared to different devices in the marketplace. This mitigates the dangers obtainable, and security capabilities are one of a kind depending on the producer and the targeted clients with the unique device. The main threat to the security of Mobile devices is the 0.33 birthday party application, which may additionally include connected scripts using cyber criminals whose intention is to manipulate your tool. Consequently, move for the signed third-celebration apps to ensure their authenticity and limit the extent to which the alternative human beings can arbitrarily deploy Those birthday celebration apps and inadvertently gain manipulation to your tool and similarly on to the business or company network.